Professional WordPress Security Testing Tool
Powerful Go application for comprehensive WordPress security analysis. Combines three key modules in one solution: WordPress discovery, credential validation, and password brute-forcing with proxy support and multi-threading.
Perfect for: penetration testers, information security specialists, web application auditors, and WordPress administrators.
Why Choose Our Tool
- ⚡ High Speed — multi-threaded processing of thousands of checks per minute
- 🌍 IDN Support — full support for internationalized domain names
- 🔒 Complete Anonymity — built-in HTTP and SOCKS proxy support
- 🎯 Maximum Accuracy — intelligent WordPress entry point detection system
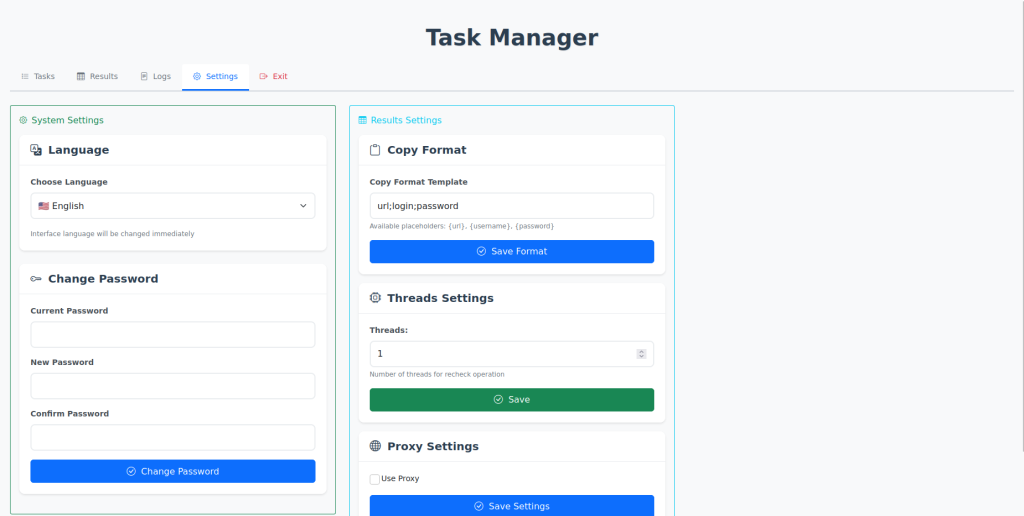
- 🔄 Flexible Configuration — customizable data formats and password templates
- 📊 Detailed Analytics — real-time statistics and monitoring
Three Powerful Modules in One Tool
🔍 1. Search — WordPress Discovery
Automatic WordPress site and user detection
The search module scans domain lists and automatically identifies WordPress sites, finds users, and detects entry points.
Key Features:
- ✅ Bulk domain scanning (including IDN domains)
- ✅ Flexible URL macros for path configuration
- ✅ Automatic user discovery via: XML Sitemap, REST API, Author pages
- ✅ Entry point detection:
wp-login.php,xmlrpc.php - ✅ Redirect handling with final URL determination
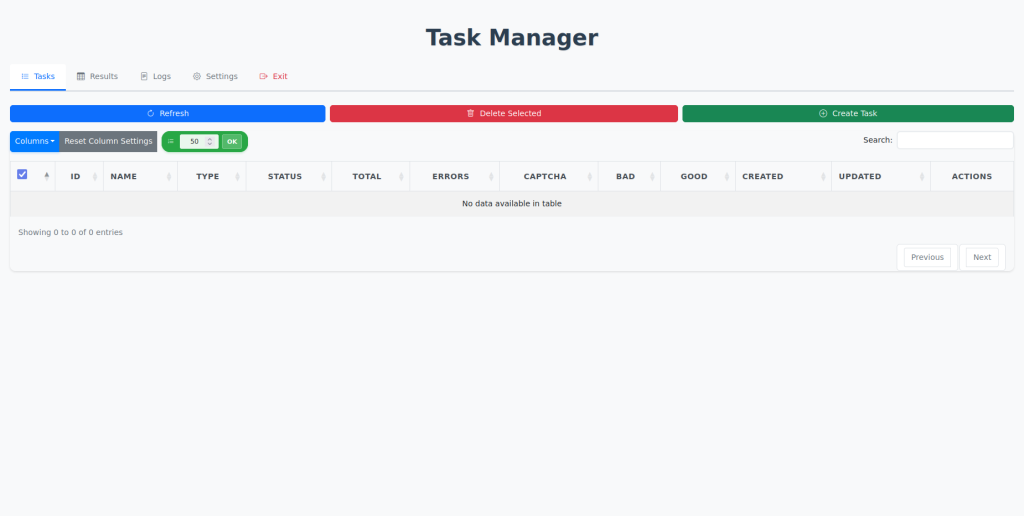
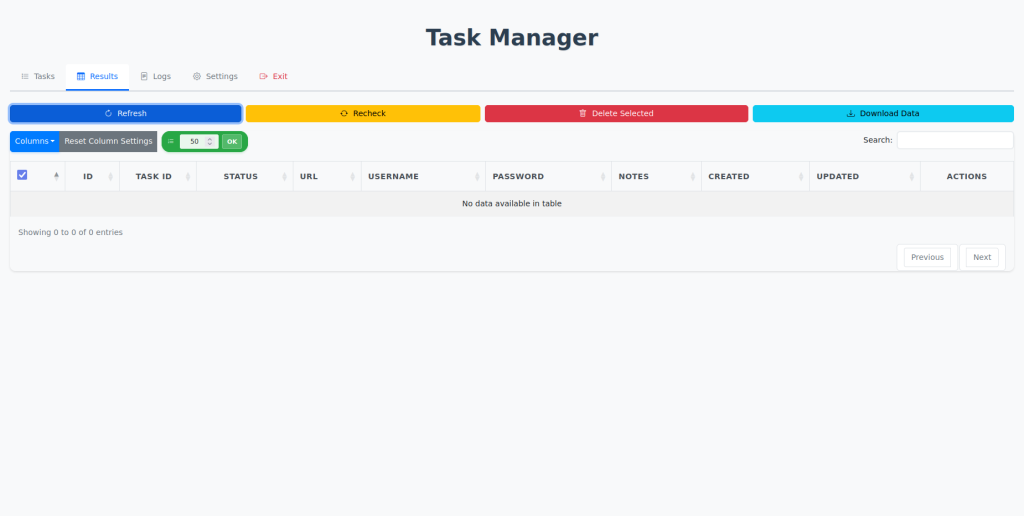
✅ 2. Checker — Credential Validation
Fast WordPress login and password verification
The checker module validates credentials via XMLRPC or standard form authentication with detailed statistics.
Key Features:
- ✅ Two authentication methods: XMLRPC, Standard form
- ✅ Bulk checking with thread configuration
- ✅ Recheck functionality
- ✅ Flexible input data formats (
URL:login:password) - ✅ Automatic CAPTCHA detection
- ✅ Detailed statistics: successful, failed, error
3. Brute — Intelligent Brute Force
Smart password generation with macros
The brute force module uses a unique macro system to generate passwords based on login and site domain.
Macro System:
| Macro | Description | Example Result |
[login] | Login in lowercase | admin |
[Login] | Capitalized first letter | Admin |
[LOGIN] | Fully uppercase | ADMIN |
[lOgIn] | Alternating case | aDmIn |
[host] | Domain without TLD | |
[Host] | Domain capitalized | |
[HOST] | Domain uppercase |
Combination Examples:
[login]123→admin123[Login]@2024→Admin@2024[HOST][login]→GOOGLEadmin[host]_[Login]!→google_Admin!
Capabilities:
- ✅ Multi-threaded password brute-forcing
- ✅ Custom templates and wordlists
- ✅ Automatic login method detection (classic, subdomain, SSO)
Additional Features
🌐 Advanced Proxy Support
- Protocol Support: HTTP, SOCKS5
- Flexible Format:
host:port:username:password - Proxy Sources: URL link to remote list, Local proxy file
- Automatic Rotation for load distribution
- Individual Settings for each task type
💻 Cross-Platform Compatibility
Windows
- Support: Windows 10/11, Server 2016+
- Required: Administrator privileges
- Auto-install to system startup
Linux
- Support: Ubuntu, Debian
- Required: Root access
- Single executable file with no dependencies
Technical Specifications
🔧 Architecture
- Development Language: Go (guaranteed high performance)
- Database: SQLite (embedded, zero-config)
- API: REST API for convenient management
- Multi-threading: Flexible thread count configuration
⚡ Performance
- Process thousands of domains per minute
- Parallel execution of multiple checks
- Minimal system resource consumption
- Real-time statistics and monitoring
Usage Examples
Scenario 1: WordPress Site Discovery
Task: Find all WordPress sites from a domain list and identify users
Input Data: domains.txt (domain list) URL Macros: https://[host]/wp-login.php Result: Discovered WordPress sites + user list
Scenario 2: Credential Validation
Task: Verify validity of login and password list
Data Format: https://site.com/wp-login.php:admin:password123 Result: Valid and invalid credentials in database
Scenario 3: Brute Force with Macros
Task: Crack password using smart templates
URL: https://example.com/wp-login.php Login: admin Templates: [login]123, [Login]@2024, [HOST][login] Result: Successful password or detailed report
System Requirements
| Component | Minimum | Recommended |
| Processor | 2 cores | 4+ cores |
| RAM | 512 MB | 2+ GB |
| Disk Space | 100 MB | 500 MB+ |
| Network | Stable connection | High-speed |
| Access Rights | Administrator/Root | Administrator/Root |
Supported OS: Windows 10/11, Server 2016+, Ubuntu, Debian